When Employees Become the Weak Link
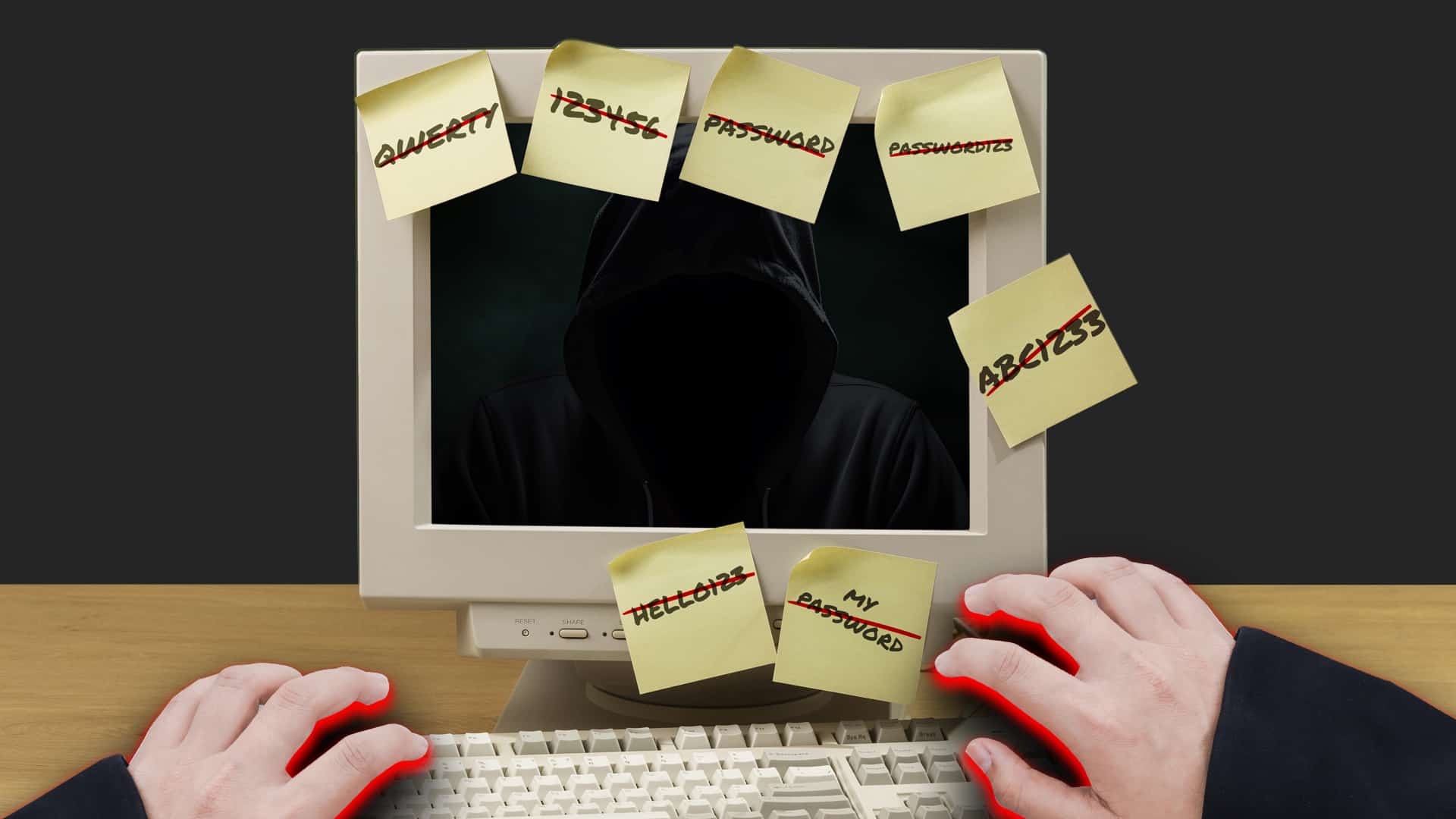
Hackers don’t need to outsmart your firewall. They just need one employee to slip up. That’s how Employees Become the Weak Link in what otherwise looks like a secure organization. A careless click. A reused password. A little too much on social media. That’s all it...